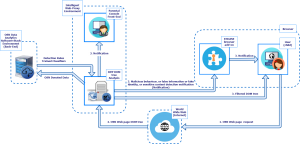
The diagram below depicts the architecture of the ENCASE Ecosystem. It is the first version of the architecture defined in the context of the Task related to the definition of the architecture and its requirements. The basic components of our architecture are: a) the client, which might be minors or their parents; b) a Web-Proxy server which will filter all the incoming and outgoing traffic of the network that the clients are connected to trying to detect Sensitive content, Malicious behavior, Fake identities and False activity based on rules generated by the Back-end of our architecture; c) a Middleware implementation which in general is part of the web-proxy functionality; and d) the Back-end of our architecture which uses machine learning and deep learning techniques to generate sophisticated rules for the detection of Malicious behavior, Fake identity and False activity detection.
The diagram will be regularly updated until we have the final version of the ENCASE Architecture.
Copyright © 2016 ENCASE

